前言: 本帖不能让你一次性成为破解大侠。
但是我们通过各种实验来推演各种复杂的变化,落点,制造不同的结局。
就像玩五子棋一样,等跳转的运用,落子的时机,顺序,棋型,走位,最终影响胜率 的不同变数。
最终我们可以总结出各种公式化、实例化,具有某种特性和规律的东西,从中享受到破解的带来奇趣 艺术体验。无论学思路,还是编程都能从中得到最大的启示。
- 强制去水印输出
- 对比走位法去时间(利用x64dbg的插件)--->扩展分支:编程实现文件夹/文件/注册表键值的监控新技能和升级《法王版x64dbg走火入魔2.0版》
- 授权的流程-->扩展分支:三度一体:编程实现《对比走位报告器2.0版》
- 强制干翻ReportForm异常(利用软件的bug)
- 解除文档为只读(编程抽码法)
- 去恶心提醒label(让软件崩溃)
- 意外获得的宝藏(伯乐识宝马篇)
- 额外的启迪与思考
每天晚上继续更新传奇故事:

这是els PJ网站上极其牛逼的软件;作为为数及其少的所见所得的CHM编辑软件,它是唯一的一款完整版的。
另外我知道的那款叫CHMEditor不少坑爹网站都用Demo版修改而成的。而今天咱们说的这个主角,则是完全版的哟~~
另外再给大家科普下,CHM编辑类软件无非分为3种:
- 第1 种是解包后编辑,诸如国内知名的SuperCHM, EasyCHM。。。太多了。
- 第2种就是咱们上面提到的。
- 第3种编辑转码或另存输出的
但是前面说的该网站上面给出的不少爆破品不少是坑爹的,是经不起时间的考验的。
我下载的算是比较新的版本吧,但是安装输出一个chm之后就会发现注册成功是假的;因为输出有乱码字符+随机水印。
于是又找零下七度表哥要了一个比较老的绿色注册版的测试;结果发现一旦输出同样有上述问题,所以,还是自己动手的最靠谱。
毕竟又有乐子,还有成就感,那自己做主的感觉就是好啊,想怎么修改就怎么修改。下面截图请出今天的主角来吧。
这个软件比较拖沓的研究了几个月时间吧,算是一个总结和交待吧,几天是不太可能全部交待明白的。所以边编辑,边修改,边总结,边说明吧。

第1章功能限制汇总与Delphi编程实现的遐想
配图

粉圈1 2 3 授权key、试用过期、未注册评估字样(其中圈3又与关于中调用的内容相同)
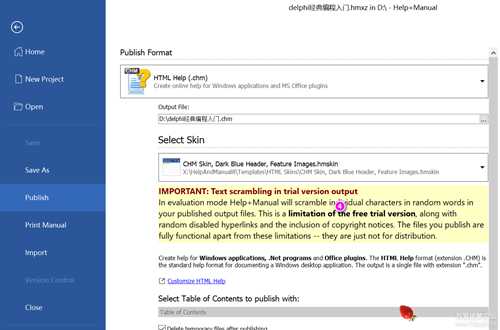
未注册发布的页面 圈 4
图圈 5(以发布*.chm文件为例)
发布后的文档
输出后的随机水印+随机字符串限制
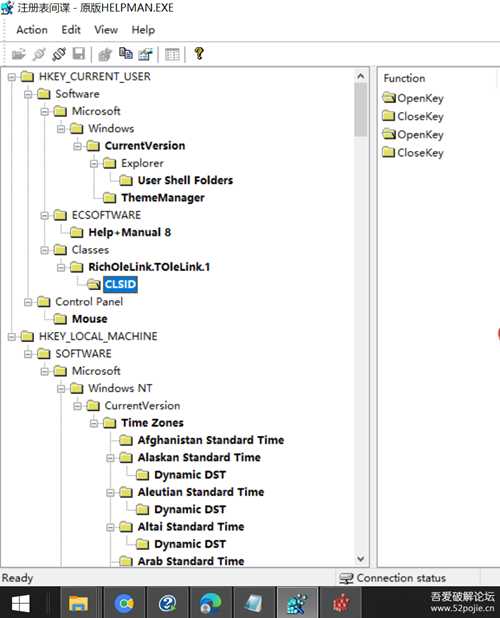
打开RegSPY一眼我就知道过期的标志是哪一个,楼下的你能说出为什么吗?
上来还是四处搜集信息,这些你都能说出个所以然来,后面的就更易理解。

第2章
输出后的随机水印+随机字符串限制

先来解决时间过期问题吧:
干掉时间限制:
- 能想到的传统方式inc 变dec
- 找到源头永远重置为空
- 使用大白补丁注入或HOOK
- 论坛bester姥爷的玩法:HOOK GetLocalTime补丁(内嵌补丁)
- 找到过期的地方修改
- 法王姥爷最爱的方式,把注册表写记号的动作干掉
可疑的几个api:
- FileTimeToLocalFileTime
- FileTimeToSystemTime
- GetLocalTime
利用插件、脚本、跟踪3种方法来对比走势和最终的分水岭。
都需要用到 1个开始的VA 和 结束的VA
猜测哪种方式更少、更快、更好?
- 开始VA、结束VA+跟踪窗对比
- 开始VA、结束VA+插件对比
- 开始VA、结束VA+脚本对比
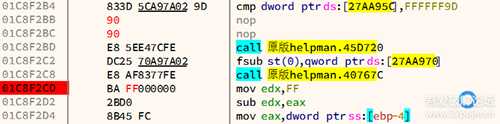
先是GetLocalTime
接着01C8F255 | E8 9A9F78FE | call <JMP.&FileTimeToSystemTime>
接着01C8F280 | E8 6F9F78FE | call <JMP.&FileTimeToSystemTime>
后面就是下面的流程了:
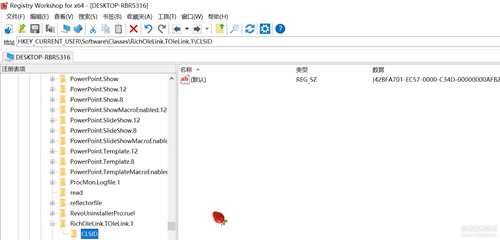
过期原因:HKEY_CURRENT_USER\Software\Classes\RichOleLink.TOleLink.1\CLSID 检测此记号
[Asm] 纯文本查看 复制代码
01B15431 | B2 01 | mov dl,1 01B15433 | A1 D41B5900 | mov eax,dword ptr ds:[591BD4] |01B15438 | E8 A3E8A7FE | call patch_bester_helpman1.593CE0 |01B1543D | 8945 EC | mov dword ptr ss:[ebp-14],eax |01B15440 | BA 01000080 | mov edx,80000001 |01B15445 | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B15448 | E8 37E9A7FE | call patch_bester_helpman1.593D84 |01B1544D | C645 EB 00 | mov byte ptr ss:[ebp-15],0 |01B15451 | 837D F8 00 | cmp dword ptr ss:[ebp-8],0 |改法1:01B15455 | 0F8E 0B010000 | jle patch_bester_helpman1.1B15566====>这里跳过01B1545B | BA 3056B101 | mov edx,patch_bester_helpman1.1B15630 | 利用字串搜索扩展插件,全局搜索那个地址常量定位到这里L"Software\\Classes\\RichOleLink.TOleLink.1"01B15460 | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B15463 | E8 48FDA7FE | call patch_bester_helpman1.5951B0 |01B15468 | 84C0 | test al,al |01B1546A | 0F84 F6000000 | je patch_bester_helpman1.1B15566 |01B15470 | 33C0 | xor eax,eax |01B15472 | 55 | push ebp |01B15473 | 68 5C55B101 | push patch_bester_helpman1.1B1555C |01B15478 | 64:FF30 | push dword ptr fs:[eax] |01B1547B | 64:8920 | mov dword ptr fs:[eax],esp |01B1547E | BA 8C56B101 | mov edx,patch_bester_helpman1.1B1568C ==>1B1568C:L"Software\\Classes\\RichOleLink.TOleLink.1\\CLSID"01B15483 | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B15486 | E8 25FDA7FE | call patch_bester_helpman1.5951B0 |01B1548B | 84C0 | test al,al |01B1548D | 0F84 BF000000 | je patch_bester_helpman1.1B15552 |01B15493 | 33C9 | xor ecx,ecx |01B15495 | BA 8C56B101 | mov edx,patch_bester_helpman1.1B1568C | 1B1568C:L"Software\\Classes\\RichOleLink.TOleLink.1\\CLSID"01B1549A | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B1549D | E8 3AEAA7FE | call patch_bester_helpman1.593EDC |01B154A2 | 84C0 | test al,al |01B154A4 | 0F84 A8000000 | je patch_bester_helpman1.1B15552 |01B154AA | 8D4D F4 | lea ecx,dword ptr ss:[ebp-C] |01B154AD | 33D2 | xor edx,edx |01B154AF | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B154B2 | E8 E1F3A7FE | call patch_bester_helpman1.594898 |01B154B7 | 33C0 | xor eax,eax |01B154B9 | 55 | push ebp |01B154BA | 68 4055B101 | push patch_bester_helpman1.1B15540 |01B154BF | 64:FF30 | push dword ptr fs:[eax] |01B154C2 | 64:8920 | mov dword ptr fs:[eax],esp |01B154C5 | 8D45 E0 | lea eax,dword ptr ss:[ebp-20] |01B154C8 | 50 | push eax |01B154C9 | B9 0C000000 | mov ecx,C | C:'\f'01B154CE | BA 1A000000 | mov edx,1A |01B154D3 | 8B45 F4 | mov eax,dword ptr ss:[ebp-C] |01B154D6 | E8 C1758FFE | call patch_bester_helpman1.40CA9C |01B154DB | 8B4D E0 | mov ecx,dword ptr ss:[ebp-20] |01B154DE | 8D45 E4 | lea eax,dword ptr ss:[ebp-1C] |01B154E1 | BA F456B101 | mov edx,patch_bester_helpman1.1B156F4 |01B154E6 | E8 E1738FFE | call patch_bester_helpman1.40C8CC |01B154EB | 8B45 E4 | mov eax,dword ptr ss:[ebp-1C] |01B154EE | E8 E13394FE | call patch_bester_helpman1.4588D4 |01B154F3 | 83E8 46 | sub eax,46 |01B154F6 | 2B45 F8 | sub eax,dword ptr ss:[ebp-8] |01B154F9 | 8945 F0 | mov dword ptr ss:[ebp-10],eax |01B154FC | 8D45 D8 | lea eax,dword ptr ss:[ebp-28] |01B154FF | 50 | push eax |01B15500 | B9 04000000 | mov ecx,4 |01B15505 | BA 15000000 | mov edx,15 |01B1550A | 8B45 F4 | mov eax,dword ptr ss:[ebp-C] |01B1550D | E8 8A758FFE | call patch_bester_helpman1.40CA9C |01B15512 | 8B4D D8 | mov ecx,dword ptr ss:[ebp-28] |01B15515 | 8D45 DC | lea eax,dword ptr ss:[ebp-24] |01B15518 | BA F456B101 | mov edx,patch_bester_helpman1.1B156F4 |01B1551D | E8 AA738FFE | call patch_bester_helpman1.40C8CC |01B15522 | 8B45 DC | mov eax,dword ptr ss:[ebp-24] |01B15525 | E8 AA3394FE | call patch_bester_helpman1.4588D4 |01B1552A | 2D 01C00000 | sub eax,C001 |01B1552F | 3B45 FC | cmp eax,dword ptr ss:[ebp-4] |01B15532 | 0F9D45 EB | setge byte ptr ss:[ebp-15] |01B15536 | 33C0 | xor eax,eax |01B15538 | 5A | pop edx |01B15539 | 59 | pop ecx |01B1553A | 59 | pop ecx |01B1553B | 64:8910 | mov dword ptr fs:[eax],edx |01B1553E | EB 0A | jmp patch_bester_helpman1.1B1554A |01B15540 | E9 B7508FFE | jmp patch_bester_helpman1.40A5FC |01B15545 | E8 CE558FFE | call patch_bester_helpman1.40AB18 |01B1554A | 8B45 EC | mov eax,dword ptr ss:[ebp-14] |01B1554D | E8 02E8A7FE | call patch_bester_helpman1.593D54 |01B15552 | 33C0 | xor eax,eax |01B15554 | 5A | pop edx |01B15555 | 59 | pop ecx |01B15556 | 59 | pop ecx |01B15557 | 64:8910 | mov dword ptr fs:[eax],edx |01B1555A | EB 0A | jmp patch_bester_helpman1.1B15566 |01B1555C | E9 9B508FFE | jmp patch_bester_helpman1.40A5FC |01B15561 | E8 B2558FFE | call patch_bester_helpman1.40AB18 |01B15566 | 807D EB 00 | cmp byte ptr ss:[ebp-15],0 |01B1556A | 75 73 | jne patch_bester_helpman1.1B155DF ===> 这里跳过!
改法2:
01C8F2AA | E8 5161E8FF | call <patch1_跳过启动注册┼无限试用.sub_1B15400> | 当然NOP上一级这个call也是成立的
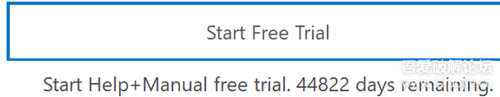
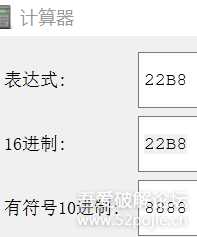
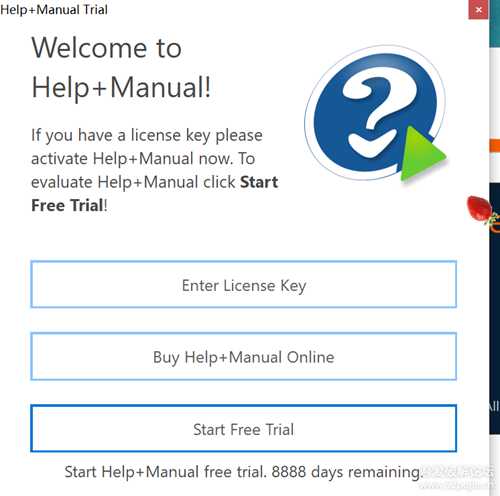
效果是永远 剩余:44822+x天
改法3:
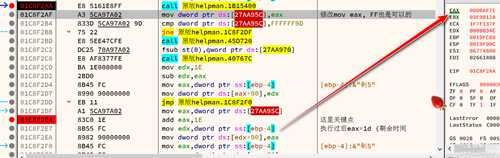
因为
01C8F2E4 | 83C0 1E | add eax,1E 执行过后eax=剩余天数
所以0x027AA95C里存的是天数
上边高亮后,看到3处
改法4:用大白补丁给 01C8F2E7这里的eax进行修改
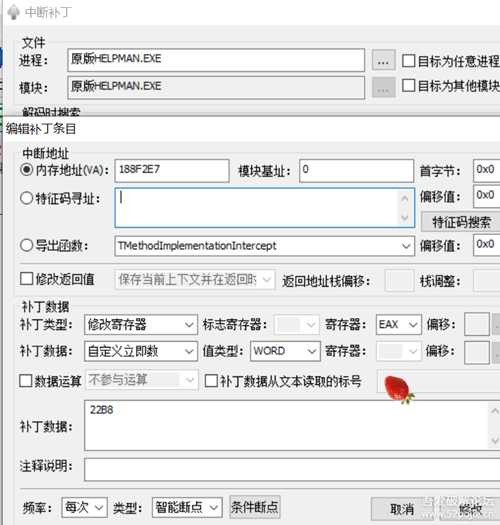
载入软件后,先bp GetLocalTime
跟踪窗口,开始跟踪
Shift+F9断下来,取消断点
Ctrl+F8让它单步步过方式运行到【未过期时的】注册窗口处
这样做的缺陷,走的太慢了
优点是不容易错过(比Ctrl+F7更快些)
这次,我们改变下策略:
不取消GetLocalTime断点
Shift+F9
Ctrl+F9 两次
Ctrl+F8
如果再遇到GetLocalTime断下时,再次Ctrl+F9 ...Ctrl+F8伺候,不再赘述
效果有改善,还是行进速度太慢!

去除水印和随机字符串限制:
Alt+E==>WriteFile下断
断到之后来到027AF9F8 kernel32.WriteFile
Ctrl+F9之后来到 :
00459020 | E8 6309FCFF call <JMP.&WriteFile> 就来到了这个关键地带
然后Ctrl+F8
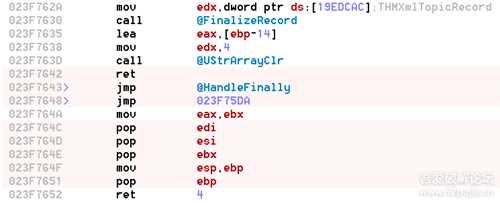
用IDR解出来的是:23F6F4C push ebp

到23F7652这结束的:
解禁思路
- 要么传送全局注册成功标志的状态
- 要么NOP掉不好的call
这里为你演示两种成功的玩法:

先思考:随机输出的垃圾字符串+垃圾块+随机禁用超链接

到底是什么?
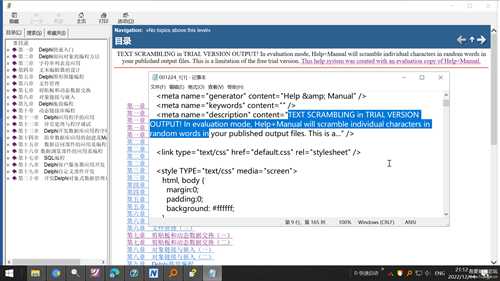
无非就是 *.html的源代码,或进一步说就是html标签
要学会进一步看到本质
到这里垃圾块的问题是不是就想通了?
随机输出的垃圾字符串?! 又是啥呢?无非是Delphi编程过程中作者设计的一个函数。
随机禁用超链接呢? 其实意思差不多。
这里把它们全部理解为:不友好的子程序(call就OK了。)
先下一个写入文件的断点
慢慢F8单步向下跟踪
直到。。。垃圾html标签的字符串现身就快到NOP掉的call位置了。
比较暴力的改法1:
[Asm] 纯文本查看 复制代码
<p class="p_Normal">TEXT SCRAMBLING in TRIAL VERSION OUTPUT! In evaluation mode, Help+Manual will scramble individual characters in random words in your published output files. This is a limitation of the free trial version. <a href="https://www." target="_blank" class="weblink"> This help system was created with an evaluation copy of Help+Manual.</a></p>UNREGISTERED EVALUATION VERSION随机乱字符串输出=============lbDemoPublish4 1fcedaalbDemoPublish 1fcf75blbDemoPublish 3c4e8a2断到了!0054586F | FF57 14 | call dword ptr ds:[edi+14] | 调用Demo的那个Label控件 lbDemoPublish==================================================Alt+E, 027AF9F8 kernel32.WriteFile断到之后,堆栈窗口之后00459020 | E8 6309FCFF | call <JMP.&WriteFile> 就来到了这个关键地带然后Ctrl+F8==================================================023F7296 | 0F85 78020000 | jne 强制去1干掉unregistered evaluation version.23F7514 | 貌似修改这JMP更好吧?023F729C | 8B07 | mov eax,dword ptr ds:[edi] |023F729E | 8B80 C8030000 | mov eax,dword ptr ds:[eax+3C8] |023F72A4 | 8B80 90000000 | mov eax,dword ptr ds:[eax+90] |023F72AA | E8 B93A9BFE | call <强制去1干掉unregistered evaluation version.sub_DAAD68 |023F72AF | BA 08000000 | mov edx,8 |023F72B4 | E8 E3D89AFE | call 强制去1干掉unregistered evaluation version.DA4B9C |023F72B9 | 8B07 | mov eax,dword ptr ds:[edi] |023F72BB | 8B80 C8030000 | mov eax,dword ptr ds:[eax+3C8] |023F72C1 | 8B80 94000000 | mov eax,dword ptr ds:[eax+94] |023F72C7 | E8 D8CB9BFE | call <强制去1干掉unregistered evaluation version.sub_DB3EA4 |023F72CC | C640 35 02 | mov byte ptr ds:[eax+35],2 |023F72D0 | 8B40 38 | mov eax,dword ptr ds:[eax+38] |023F72D3 | 8B40 14 | mov eax,dword ptr ds:[eax+14] |023F72D6 | C640 04 01 | mov byte ptr ds:[eax+4],1 |023F72DA | 55 | push ebp |不如这个上面几行的吧?023F72DB | E8 3CFCFFFF | call <patch1_跳过启动注册┼无限试用1.sub_23F6F1C> ==>右边这里有写入评估水印之类的字符串(粘贴bug过不来)023F72E0 | 59 | pop ecx |023F72E1 | 84C0 | test al,al |023F72E3 | 0F84 F1000000 | je patch1_跳过启动注册┼无限试用1.23F73DA ===>▲修改这里【未注册字符串的写入】NOP掉!023F72E9 | 8B07 | mov eax,dword ptr ds:[edi] | [edi]:&"\f沶"023F72EB | 8B80 C8030000 | mov eax,dword ptr ds:[eax+3C8] |023F72F1 | 8B90 94000000 | mov edx,dword ptr ds:[eax+94] |023F72F7 | 8B52 08 | mov edx,dword ptr ds:[edx+8] |023F72FA | 8B52 08 | mov edx,dword ptr ds:[edx+8] |023F72FD | 4A | dec edx |023F72FE | 52 | push edx |023F72FF | 6A 00 | push 0 |023F7301 | 8B80 90000000 | mov eax,dword ptr ds:[eax+90] |023F7307 | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F730A | 8B48 08 | mov ecx,dword ptr ds:[eax+8] |023F730D | 49 | dec ecx |023F730E | 8B07 | mov eax,dword ptr ds:[edi] | [edi]:&"\f沶"023F7310 | 8B80 C0030000 | mov eax,dword ptr ds:[eax+3C0] |023F7316 | 33D2 | xor edx,edx |023F7318 | E8 A76395FE | call <patch1_跳过启动注册┼无限试用1.sub_D4D6C4> |023F731D | 8B07 | mov eax,dword ptr ds:[edi] | [edi]:&"\f沶"023F731F | 8BB0 C8030000 | mov esi,dword ptr ds:[eax+3C8] | esi:&"劋S"023F7325 | 8B86 94000000 | mov eax,dword ptr ds:[esi+94] |023F732B | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F732E | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F7331 | 48 | dec eax |023F7332 | 50 | push eax |023F7333 | 68 D8773F02 | push patch1_跳过启动注册┼无限试用1.23F77D8 | 23F77D8:L"DISPLAY="023F7338 | 8D55 98 | lea edx,dword ptr ss:[ebp-68] |023F733B | 33C0 | xor eax,eax |023F733D | E8 261306FE | call <patch1_跳过启动注册┼无限试用1.sub_458668> |023F7342 | FF75 98 | push dword ptr ss:[ebp-68] |023F7345 | 68 F8773F02 | push patch1_跳过启动注册┼无限试用1.23F77F8 |023F734A | 68 08783F02 | push patch1_跳过启动注册┼无限试用1.23F7808 | 23F7808:L"VALID=1"023F734F | 68 F8773F02 | push patch1_跳过启动注册┼无限试用1.23F77F8 |023F7354 | 68 24783F02 | push patch1_跳过启动注册┼无限试用1.23F7824 | 23F7824:L"TYPE="023F7359 | 8D55 94 | lea edx,dword ptr ss:[ebp-6C] |023F735C | B8 01000000 | mov eax,1 |023F7361 | E8 021306FE | call <patch1_跳过启动注册┼无限试用1.sub_458668> |023F7366 | FF75 94 | push dword ptr ss:[ebp-6C] |023F7369 | 68 F8773F02 | push patch1_跳过启动注册┼无限试用1.23F77F8 |023F736E | 68 3C783F02 | push patch1_跳过启动注册┼无限试用1.23F783C | 23F783C:L"DATA="023F7373 | 68 54783F02 | push <patch1_跳过启动注册┼无限试用1.sub_23F7854> | 23F7854:L"T=https://www."023F7378 | 68 A0783F02 | push patch1_跳过启动注册┼无限试用1.23F78A0 | 23F78A0:L"\r\n"023F737D | 68 B4783F02 | push patch1_跳过启动注册┼无限试用1.23F78B4 | 23F78B4:L"W=_blank"023F7382 | 8D45 9C | lea eax,dword ptr ss:[ebp-64] |023F7385 | BA 0C000000 | mov edx,C | C:'\f'23F6F1C这个call F7进入后,发现:023F6F22 | 8D45 F8 | lea eax,dword ptr ss:[ebp-8] | [ebp-8]:L"idh_class_tcustomrvparainfo" 显然是Delphi中的自定义控件类023F7245 | 85C0 | test eax,eax | eax:&L"TEXT SCRAMBLING in TRIAL VERSION OUTPUT! In evaluation mode, Help+Manual will scramble individual characters in random words in your published output files. This is a limitation of the free trial version. "=========================================02396299 | 8B80 E8010000 | mov eax,dword ptr ds:[eax+1E8] | eax:&"劋S", [eax+1E8]:"447858949346180"0239629F | 33D2 | xor edx,edx |023962A1 | E8 2A9D3FFE | call patch1_跳过启动注册.78FFD0 |023962A6 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962A9 | 8B80 E8010000 | mov eax,dword ptr ds:[eax+1E8] | eax:&"劋S", [eax+1E8]:"447858949346180"023962AF | E8 F0723FFE | call patch1_跳过启动注册.78D5A4 |023962B4 | 84C0 | test al,al |023962B6 | 75 1F | jne patch1_跳过启动注册.23962D7 |023962B8 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962BB | 8B80 E8010000 | mov eax,dword ptr ds:[eax+1E8] | eax:&"劋S", [eax+1E8]:"447858949346180"023962C1 | E8 C2430CFE | call patch1_跳过启动注册.45A688 |023962C6 | 84C0 | test al,al |023962C8 | 75 0D | jne patch1_跳过启动注册.23962D7 |023962CA | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962CD | 05 E8010000 | add eax,1E8 | eax:&"劋S"023962D2 | E8 715107FE | call patch1_跳过启动注册.40B448 |023962D7 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962DA | 83B8 E8010000 00 | cmp dword ptr ds:[eax+1E8],0 | [eax+1E8]:"447858949346180"023962E1 | 0F9585 4FFFFFFF | setne byte ptr ss:[ebp-B1] |023962E8 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962EB | 05 EC010000 | add eax,1EC | eax:&"劋S"023962F0 | 8B55 FC | mov edx,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023962F3 | 8B92 E8010000 | mov edx,dword ptr ds:[edx+1E8] |023962F9 | E8 2A5507FE | call patch1_跳过启动注册.40B828 |023962FE | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396301 | 05 F4010000 | add eax,1F4 | eax:&"劋S"02396306 | 8B55 FC | mov edx,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396309 | 8B92 E8010000 | mov edx,dword ptr ds:[edx+1E8] |0239630F | E8 145507FE | call patch1_跳过启动注册.40B828 |02396314 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396317 | 05 F0010000 | add eax,1F0 | eax:&"劋S"0239631C | 8B55 FC | mov edx,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"0239631F | 8B92 E8010000 | mov edx,dword ptr ds:[edx+1E8] |02396325 | E8 FE5407FE | call patch1_跳过启动注册.40B828 |0239632A | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"0239632D | 8B90 E8010000 | mov edx,dword ptr ds:[eax+1E8] | [eax+1E8]:"447858949346180"02396333 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396336 | 05 F8010000 | add eax,1F8 | eax:&"劋S"0239633B | B9 FC933902 | mov ecx,patch1_跳过启动注册.23993FC | ecx:&"劋S", 23993FC:L"\\xplain"02396340 | E8 876507FE | call patch1_跳过启动注册.40C8CC |02396345 | 80BD 4FFFFFFF 00 | cmp byte ptr ss:[ebp-B1],0 |0239634C | 75 32 | jne patch1_跳过启动注册.2396380 |0239634E | 8D85 8CFEFFFF | lea eax,dword ptr ss:[ebp-174] |02396354 | 50 | push eax | eax:&"劋S"02396355 | 6A FF | push FFFFFFFF |02396357 | 6A 00 | push 0 |02396359 | 8D95 34FBFFFF | lea edx,dword ptr ss:[ebp-4CC] |0239635F | B8 E0423802 | mov eax,patch1_跳过启动注册.23842E0 | eax:&"劋S"02396364 | E8 D79C07FE | call patch1_跳过启动注册.410040 |02396369 | 8B8D 34FBFFFF | mov ecx,dword ptr ss:[ebp-4CC] |0239636F | A1 10857502 | mov eax,dword ptr ds:[2758510] | eax:&"劋S"02396374 | 8B00 | mov eax,dword ptr ds:[eax] | eax:&"劋S", [eax]:"劋S"02396376 | BA B80B0000 | mov edx,BB8 |0239637B | E8 900D0700 | call patch1_跳过启动注册.2407110 | --->关注这里!!!!02396380 | 80BD 4FFFFFFF 00 | cmp byte ptr ss:[ebp-B1],0 |02396387 | 0F84 040A0000 | je patch1_跳过启动注册.2396D91 |0239638D | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396390 | C680 D1010000 01 | mov byte ptr ds:[eax+1D1],1 |02396397 | A1 10857502 | mov eax,dword ptr ds:[2758510] | eax:&"劋S"0239639C | 8B00 | mov eax,dword ptr ds:[eax] | eax:&"劋S", [eax]:"劋S"0239639E | 8B80 F0030000 | mov eax,dword ptr ds:[eax+3F0] | eax:&"劋S"023963A4 | E8 FB9374FF | call patch1_跳过启动注册.1ADF7A4 |023963A9 | 8BD8 | mov ebx,eax | eax:&"劋S"023963AB | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023963AE | 8998 CC000000 | mov dword ptr ds:[eax+CC],ebx |023963B4 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023963B7 | 80B8 CB010000 00 | cmp byte ptr ds:[eax+1CB],0 |023963BE | 0F84 B4090000 | je patch1_跳过启动注册.2396D78 |023963C4 | 8BC3 | mov eax,ebx | eax:&"劋S"023963C6 | E8 8D9774FF | call patch1_跳过启动注册.1ADFB58 |023963CB | 85C0 | test eax,eax | eax:&"劋S"023963CD | 0F84 A5090000 | je patch1_跳过启动注册.2396D78 |023963D3 | 8D85 8CFEFFFF | lea eax,dword ptr ss:[ebp-174] |023963D9 | 50 | push eax | eax:&"劋S"023963DA | 6A FF | push FFFFFFFF |023963DC | 6A 00 | push 0 |023963DE | 8D95 30FBFFFF | lea edx,dword ptr ss:[ebp-4D0] |023963E4 | B8 D8423802 | mov eax,patch1_跳过启动注册.23842D8 | eax:&"劋S"023963E9 | E8 529C07FE | call patch1_跳过启动注册.410040 |023963EE | 8B8D 30FBFFFF | mov ecx,dword ptr ss:[ebp-4D0] |023963F4 | A1 10857502 | mov eax,dword ptr ds:[2758510] | eax:&"劋S"023963F9 | 8B00 | mov eax,dword ptr ds:[eax] | eax:&"劋S", [eax]:"劋S"023963FB | BA B80B0000 | mov edx,BB8 |02396400 | E8 0B0D0700 | call patch1_跳过启动注册.2407110 |02396405 | C685 4FFFFFFF 00 | mov byte ptr ss:[ebp-B1],0 |0239640C | E9 67090000 | jmp patch1_跳过启动注册.2396D78 |02396411 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396414 | 8B88 D8010000 | mov ecx,dword ptr ds:[eax+1D8] | ecx:&"劋S"0239641A | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"0239641D | 8B80 DC010000 | mov eax,dword ptr ds:[eax+1DC] | eax:&"劋S"02396423 | BA 64000000 | mov edx,64 | 64:'d'02396428 | E8 6BF364FF | call patch1_跳过启动注册.19E5798 |0239642D | 50 | push eax | eax:&"劋S"0239642E | 8D85 4FFFFFFF | lea eax,dword ptr ss:[ebp-B1] |02396434 | 50 | push eax | eax:&"劋S"02396435 | 8D95 2CFBFFFF | lea edx,dword ptr ss:[ebp-4D4] |0239643B | B8 F0423802 | mov eax,patch1_跳过启动注册.23842F0 | eax:&"劋S"02396440 | E8 FB9B07FE | call patch1_跳过启动注册.410040 |02396445 | 8D85 2CFBFFFF | lea eax,dword ptr ss:[ebp-4D4] |0239644B | 8B55 FC | mov edx,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"0239644E | 8B92 CC000000 | mov edx,dword ptr ds:[edx+CC] |02396454 | 8B52 38 | mov edx,dword ptr ds:[edx+38] |02396457 | 8B52 04 | mov edx,dword ptr ds:[edx+4] |0239645A | E8 156407FE | call patch1_跳过启动注册.40C874 |0239645F | 8B85 2CFBFFFF | mov eax,dword ptr ss:[ebp-4D4] |02396465 | 50 | push eax | eax:&"劋S"02396466 | 8D95 28FBFFFF | lea edx,dword ptr ss:[ebp-4D8] |0239646C | B8 E8423802 | mov eax,patch1_跳过启动注册.23842E8 | eax:&"劋S"02396471 | E8 CA9B07FE | call patch1_跳过启动注册.410040 |02396476 | 8B95 28FBFFFF | mov edx,dword ptr ss:[ebp-4D8] |0239647C | 59 | pop ecx | ecx:&"劋S"0239647D | 8B05 94C57A02 | mov eax,dword ptr ds:[27AC594] | eax:&"劋S"02396483 | FF15 90C57A02 | call dword ptr ds:[27AC590] |02396489 | 80BD 4FFFFFFF 00 | cmp byte ptr ss:[ebp-B1],0 |02396490 | 0F84 55070000 | je patch1_跳过启动注册.2396BEB |02396496 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"02396499 | 8B80 CC000000 | mov eax,dword ptr ds:[eax+CC] | eax:&"劋S"0239649F | E8 289074FF | call patch1_跳过启动注册.1ADF4CC |023964A4 | 48 | dec eax | eax:&"劋S"023964A5 | 0F85 40070000 | jne patch1_跳过启动注册.2396BEB |023964AB | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023964AE | 8B80 CC000000 | mov eax,dword ptr ds:[eax+CC] | eax:&"劋S"023964B4 | 8B50 3C | mov edx,dword ptr ds:[eax+3C] |023964B7 | 33C9 | xor ecx,ecx | ecx:&"劋S"023964B9 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023964BC | E8 3FE7FBFF | call patch1_跳过启动注册.2354C00 |023964C1 | 84C0 | test al,al |023964C3 | 0F85 22070000 | jne patch1_跳过启动注册.2396BEB |023964C9 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023964CC | FF80 DC010000 | inc dword ptr ds:[eax+1DC] |023964D2 | 6A 01 | push 1 |023964D4 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023964D7 | 8B80 CC000000 | mov eax,dword ptr ds:[eax+CC] | eax:&"劋S"023964DD | 8B48 3C | mov ecx,dword ptr ds:[eax+3C] | ecx:&"劋S"023964E0 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"023964E3 | 8B80 CC000000 | mov eax,dword ptr ds:[eax+CC] | eax:&"劋S"023964E9 | 8B50 78 | mov edx,dword ptr ds:[eax+78] |023964EC | A1 10857502 | mov eax,dword ptr ds:[2758510] | eax:&"劋S"023964F1 | 8B00 | mov eax,dword ptr ds:[eax] | eax:&"劋S", [eax]:"劋S"023964F3 | E8 540A0600 | call patch1_跳过启动注册.23F6F4C | =============>里边有那个未注册字符调用1)023964F8 | 84C0 | test al,al |023964FA | 0F84 3F060000 | je patch1_跳过启动注册.2396B3F |$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$023F7409 | 8B55 84 | mov edx,dword ptr ss:[ebp-7C] | ▲▲▲我烤,原来你在这里啦!!!TEXT SCRAMBLING in TRIAL VERSION OUTPUT! In evaluation mode, Help+Manual will scramble individual characters in random words in your published output files. This is a limitation of the free trial version. "023F740C | 8D45 88 | lea eax,dword ptr ss:[ebp-78] |023F740F | E8 245301FE | call patch1_跳过启动注册.40C738 |023F7414 | 8B55 88 | mov edx,dword ptr ss:[ebp-78] |023F7417 | 8B07 | mov eax,dword ptr ds:[edi] | [edi]:&"\f沶"023F7419 | 8B80 C0030000 | mov eax,dword ptr ds:[eax+3C0] |023F741F | 33C9 | xor ecx,ecx |023F7421 | E8 02758EFE | call patch1_跳过启动注册.CDE928 |$$$$$$$$$$023F72E3 | 0F84 F1000000 | je patch1_跳过启动注册.23F73DA | 设为B1(此处实现就完犊子了!!!)▲可以干掉顶部的那个TEXT SCRAMBLING in TRIAL VERSION OUTPUT! 023F72E9 | 8B07 | mov eax,dword ptr ds:[edi] | eax:L"in-familysafety-childaccount-l1-1-0", edi:"U嬱笿"023F72EB | 8B80 C8030000 | mov eax,dword ptr ds:[eax+3C8] | eax:L"in-familysafety-childaccount-l1-1-0", [eax+3C8]:sub_78005F+6023F72F1 | 8B90 94000000 | mov edx,dword ptr ds:[eax+94] | eax+94:L"in-feclient-encryptedfile-l1-1-3"023F72F7 | 8B52 08 | mov edx,dword ptr ds:[edx+8] |023F72FA | 8B52 08 | mov edx,dword ptr ds:[edx+8] |====================================================================================cmp dword ptr ds:[eax+0x28], 0x1 反转也可跳过过期 和 部分时间限制!cmp dword ptr ds:[eax+0x28], 0x0向下跟发现的向下跟发现的02661A9E mov edx, 0x2662D44 LicMode:%s This help system was created with an evaluation copy of Help+Manual. 这玩意 也得干掉!-------------------------------------------------------------------------------------------------------00459020 | E8 6309FCFF | call <JMP.&WriteFile> 就来到了这个关键地带然后Ctrl+F8023F716F | 0F95C0 | setne al ====>反转成94023F7172 | 2245 08 | and al,byte ptr ss:[ebp+8] 023F72E3 | 90 | nop | 我们从这里开始NOP023F72E4 | 90 | nop |023F72E5 | 90 | nop |023F72E6 | 90 | nop |023F72E7 | 90 | nop |023F72E8 | 90 | nop |023F72E9 | 8B07 | mov eax,dword ptr ds:[edi] | edi:"U嬱笿"023F72EB | 8B80 C8030000 | mov eax,dword ptr ds:[eax+3C8] |023F72F1 | 8B90 94000000 | mov edx,dword ptr ds:[eax+94] |023F72F7 | 8B52 08 | mov edx,dword ptr ds:[edx+8] |023F72FA | 8B52 08 | mov edx,dword ptr ds:[edx+8] |023F72FD | 4A | dec edx |023F72FE | 52 | push edx |023F72FF | 6A 00 | push 0 |023F7301 | 8B80 90000000 | mov eax,dword ptr ds:[eax+90] |023F7307 | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F730A | 8B48 08 | mov ecx,dword ptr ds:[eax+8] |023F730D | 49 | dec ecx |023F730E | 8B07 | mov eax,dword ptr ds:[edi] | edi:"U嬱笿"023F7310 | 8B80 C0030000 | mov eax,dword ptr ds:[eax+3C0] |023F7316 | 33D2 | xor edx,edx |023F7318 | E8 A76395FE | call 4554454545545445455454.D4D6C4 |023F731D | 8B07 | mov eax,dword ptr ds:[edi] | edi:"U嬱笿"023F731F | 8BB0 C8030000 | mov esi,dword ptr ds:[eax+3C8] | esi:"U嬱笿"023F7325 | 8B86 94000000 | mov eax,dword ptr ds:[esi+94] |023F732B | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F732E | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F7331 | 48 | dec eax |023F7332 | 50 | push eax |023F7333 | 68 D8773F02 | push 4554454545545445455454.23F77D8 | 23F77D8:L"DISPLAY="023F7338 | 8D55 98 | lea edx,dword ptr ss:[ebp-68] | [ebp-68]:"U嬱笿"023F733B | 33C0 | xor eax,eax |023F733D | E8 261306FE | call 4554454545545445455454.458668 |023F7342 | FF75 98 | push dword ptr ss:[ebp-68] | [ebp-68]:"U嬱笿"023F7345 | 68 F8773F02 | push 4554454545545445455454.23F77F8 |023F734A | 68 08783F02 | push 4554454545545445455454.23F7808 | 23F7808:L"VALID=1"023F734F | 68 F8773F02 | push 4554454545545445455454.23F77F8 |023F7354 | 68 24783F02 | push 4554454545545445455454.23F7824 | 23F7824:L"TYPE="023F7359 | 8D55 94 | lea edx,dword ptr ss:[ebp-6C] |023F735C | B8 01000000 | mov eax,1 |023F7361 | E8 021306FE | call 4554454545545445455454.458668 |023F7366 | FF75 94 | push dword ptr ss:[ebp-6C] |023F7369 | 68 F8773F02 | push 4554454545545445455454.23F77F8 |023F736E | 68 3C783F02 | push 4554454545545445455454.23F783C | 23F783C:L"DATA="023F7373 | 68 54783F02 | push 4554454545545445455454.23F7854 | 23F7854:L"T=https://www."023F7378 | 68 A0783F02 | push 4554454545545445455454.23F78A0 | 23F78A0:L"\r\n"023F737D | 68 B4783F02 | push 4554454545545445455454.23F78B4 | 23F78B4:L"W=_blank"023F7382 | 8D45 9C | lea eax,dword ptr ss:[ebp-64] |023F7385 | BA 0C000000 | mov edx,C | C:'\f'023F738A | E8 C55501FE | call 4554454545545445455454.40C954 |023F738F | 8B45 9C | mov eax,dword ptr ss:[ebp-64] |023F7392 | 50 | push eax |023F7393 | 8D4D 8C | lea ecx,dword ptr ss:[ebp-74] |023F7396 | A1 5CB37502 | mov eax,dword ptr ds:[275B35C] |023F739B | 8B00 | mov eax,dword ptr ds:[eax] |023F739D | 8B80 94000000 | mov eax,dword ptr ds:[eax+94] |023F73A3 | BA D4783F02 | mov edx,4554454545545445455454.23F7 |023F73A8 | E8 377938FE | call 4554454545545445455454.77ECE4 |023F73AD | 8B55 8C | mov edx,dword ptr ss:[ebp-74] |023F73B0 | 8D45 90 | lea eax,dword ptr ss:[ebp-70] |023F73B3 | E8 805301FE | call 4554454545545445455454.40C738 |023F73B8 | 8B55 90 | mov edx,dword ptr ss:[ebp-70] |023F73BB | 8B86 90000000 | mov eax,dword ptr ds:[esi+90] |023F73C1 | 8B40 08 | mov eax,dword ptr ds:[eax+8] |023F73C4 | 8B48 08 | mov ecx,dword ptr ds:[eax+8] |023F73C7 | 49 | dec ecx |023F73C8 | 8B07 | mov eax,dword ptr ds:[edi] | edi:"U嬱笿"023F73CA | 8B80 C0030000 | mov eax,dword ptr ds:[eax+3C0] |023F73D0 | E8 EF6295FE | call 4554454545545445455454.D4D6C4 JMP(到此处的上行结束!)
爆破方式2: 0F95C0 setne al 反转此处,因为为最上级,因此下面的流程走向都会被影响到,所以立竿见影。
爆破方式3: 直接给注册表取键值后返回1,目前还没找到,不过按经验来说必然是成立的。
爆破水印的功能仅用时15分钟就解决困扰了。
一般输出是没啥影响的。。。。但是!!! 一旦载入example的树状的js调用的代码(X:\HelpAndManual6\Examples\Get Me Started Example\Get_Me_Started.hmxz),
就会有js调用不正常的网页框出现

。。。
还是老办法,把*.chm 解出来,变成 看得见的*.html 文件,查看源代码
这里可以照样 6.0 去暗桩正常的输出 与 不正常的输出对照着看,修补下我们的补丁程序。。。
激活按钮不可用
诡异的cmd授权窗口
授权信息
注册码的两种存放形式与位置:
A.注册表键值
B.主程序名+.lic

6.0版的授权流程比较简单:
[Asm] 纯文本查看 复制代码
013E21CA | 8038 00 | cmp byte ptr ds:[eax],0 |013E21CD | 0F84 41020000 | je helpman.13E2414 | 这里跳了,注册不注册都一样013E21D3 | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E21D8 | C600 00 | mov byte ptr ds:[eax],0 |013E21DB | 8D55 E0 | lea edx,dword ptr ss:[ebp-20] |013E21DE | B8 02000000 | mov eax,2 |013E21E3 | E8 EC2702FF | call helpman.4049D4 |013E21E8 | 8B45 E0 | mov eax,dword ptr ss:[ebp-20] |013E21EB | BA 8C253E01 | mov edx,helpman.13E258C | 13E258C:L"/fc"013E21F0 | E8 2B6D02FF | call helpman.408F20 |013E21F5 | 74 15 | je helpman.13E220C |013E21F7 | 6A FF | push FFFFFFFF |013E21F9 | A1 E8384601 | mov eax,dword ptr ds:[14638E8] |013E21FE | 8B00 | mov eax,dword ptr ds:[eax] |013E2200 | FFD0 | call eax |013E2202 | 85C0 | test eax,eax |013E2204 | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2209 | 0F9500 | setne byte ptr ds:[eax] |013E220C | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2211 | 8038 00 | cmp byte ptr ds:[eax],0 |013E2214 | 74 47 | je helpman.13E225D |013E2216 | 33C0 | xor eax,eax |013E2218 | 55 | push ebp |013E2219 | 68 46223E01 | push helpman.13E2246 |013E221E | 64:FF30 | push dword ptr fs:[eax] |013E2221 | 64:8920 | mov dword ptr fs:[eax],esp |013E2224 | A1 EC464601 | mov eax,dword ptr ds:[14646EC] |013E2229 | 66:BA 2000 | mov dx,20 | 20:' '013E222D | E8 AE3402FF | call helpman.4056E0 |013E2232 | E8 492D02FF | call helpman.404F80 |013E2237 | E8 B02402FF | call helpman.4046EC |013E223C | 33C0 | xor eax,eax |013E223E | 5A | pop edx |013E223F | 59 | pop ecx |013E2240 | 59 | pop ecx |013E2241 | 64:8910 | mov dword ptr fs:[eax],edx |013E2244 | EB 17 | jmp helpman.13E225D |013E2246 | E9 F94902FF | jmp helpman.406C44 |013E224B | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2250 | C600 00 | mov byte ptr ds:[eax],0 |013E2253 | E8 4CD102FF | call <JMP.&FreeConsole> |013E2258 | E8 034F02FF | call helpman.407160 |013E225D | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2262 | 8038 00 | cmp byte ptr ds:[eax],0 |013E2265 | 75 13 | jne helpman.13E227A |013E2267 | E8 B8CF02FF | call <JMP.&AllocConsole> |013E226C | 83F8 01 | cmp eax,1 |013E226F | 1BC0 | sbb eax,eax |013E2271 | 40 | inc eax |013E2272 | 8B15 94404601 | mov edx,dword ptr ds:[1464094] |013E2278 | 8802 | mov byte ptr ds:[edx],al |013E227A | 33D2 | xor edx,edx |013E227C | 55 | push ebp |013E227D | 68 0D243E01 | push helpman.13E240D |013E2282 | 64:FF32 | push dword ptr fs:[edx] |013E2285 | 64:8922 | mov dword ptr fs:[edx],esp |013E2288 | 8B0D BC574601 | mov ecx,dword ptr ds:[14657BC] |013E228E | 8B09 | mov ecx,dword ptr ds:[ecx] |013E2290 | B2 01 | mov dl,1 |013E2292 | A1 3CE7F000 | mov eax,dword ptr ds:[F0E73C] | 00F0E73C:&"砾D"013E2297 | E8 60DEB2FF | call helpman.F100FC |013E229C | 8B15 185A4601 | mov edx,dword ptr ds:[1465A18] |013E22A2 | 8902 | mov dword ptr ds:[edx],eax |013E22A4 | 33D2 | xor edx,edx |013E22A6 | 55 | push ebp |013E22A7 | 68 E9233E01 | push helpman.13E23E9 |013E22AC | 64:FF32 | push dword ptr fs:[edx] |013E22AF | 64:8922 | mov dword ptr fs:[edx],esp |013E22B2 | 8B0D B03A4601 | mov ecx,dword ptr ds:[1463AB0] |013E22B8 | A1 BC574601 | mov eax,dword ptr ds:[14657BC] |013E22BD | 8B00 | mov eax,dword ptr ds:[eax] |013E22BF | 8B15 ACA22C01 | mov edx,dword ptr ds:[12CA2AC] | 012CA2AC:&"悂J"013E22C5 | E8 DEFA16FF | call helpman.551DA8 |013E22CA | 33D2 | xor edx,edx |013E22CC | 55 | push ebp |013E22CD | 68 BE233E01 | push helpman.13E23BE |013E22D2 | 64:FF32 | push dword ptr fs:[edx] |013E22D5 | 64:8922 | mov dword ptr fs:[edx],esp |013E22D8 | A1 78454601 | mov eax,dword ptr ds:[1464578] |013E22DD | C600 00 | mov byte ptr ds:[eax],0 |013E22E0 | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E22E5 | 8038 00 | cmp byte ptr ds:[eax],0 |013E22E8 | 0F84 A0000000 | je helpman.13E238E |013E22EE | 33C0 | xor eax,eax |013E22F0 | 55 | push ebp |013E22F1 | 68 7C233E01 | push helpman.13E237C |013E22F6 | 64:FF30 | push dword ptr fs:[eax] |013E22F9 | 64:8920 | mov dword ptr fs:[eax],esp |013E22FC | 68 A0253E01 | push helpman.13E25A0 | 13E25A0:"Help & Manual command line compiler version "013E2301 | A1 185A4601 | mov eax,dword ptr ds:[1465A18] |013E2306 | 8B00 | mov eax,dword ptr ds:[eax] |013E2308 | FF70 74 | push dword ptr ds:[eax+74] |013E230B | 68 DC253E01 | push helpman.13E25DC | 13E25DC:" build "013E2310 | A1 185A4601 | mov eax,dword ptr ds:[1465A18] |013E2315 | 8B00 | mov eax,dword ptr ds:[eax] |013E2317 | FF70 78 | push dword ptr ds:[eax+78] |013E231A | 8D45 DC | lea eax,dword ptr ss:[ebp-24] |013E231D | BA 04000000 | mov edx,4 |013E2322 | E8 D15F02FF | call helpman.4082F8 |013E2327 | 8B55 DC | mov edx,dword ptr ss:[ebp-24] |013E232A | A1 EC464601 | mov eax,dword ptr ds:[14646EC] |013E232F | E8 903202FF | call helpman.4055C4 |013E2334 | E8 133402FF | call helpman.40574C |013E2339 | E8 AE2302FF | call helpman.4046EC |013E233E | 8D55 D4 | lea edx,dword ptr ss:[ebp-2C] |013E2341 | B8 01000000 | mov eax,1 |013E2346 | E8 892602FF | call helpman.4049D4 |013E234B | 8B4D D4 | mov ecx,dword ptr ss:[ebp-2C] |013E234E | 8D45 D8 | lea eax,dword ptr ss:[ebp-28] |013E2351 | BA F0253E01 | mov edx,helpman.13E25F0 | 13E25F0:L"Compiling "013E2356 | E8 2D6A02FF | call helpman.408D88 |013E235B | 8B55 D8 | mov edx,dword ptr ss:[ebp-28] |013E235E | A1 EC464601 | mov eax,dword ptr ds:[14646EC] |013E2363 | E8 883202FF | call helpman.4055F0 |013E2368 | E8 DF3302FF | call helpman.40574C |013E236D | E8 7A2302FF | call helpman.4046EC |013E2372 | 33C0 | xor eax,eax |013E2374 | 5A | pop edx |013E2375 | 59 | pop ecx |013E2376 | 59 | pop ecx |013E2377 | 64:8910 | mov dword ptr fs:[eax],edx |013E237A | EB 12 | jmp helpman.13E238E |013E237C | E9 C34802FF | jmp helpman.406C44 |013E2381 | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2386 | C600 00 | mov byte ptr ds:[eax],0 |013E2389 | E8 D24D02FF | call helpman.407160 |013E238E | A1 B03A4601 | mov eax,dword ptr ds:[1463AB0] |013E2393 | 8B00 | mov eax,dword ptr ds:[eax] |013E2395 | E8 B6FFF1FF | call helpman.1302350 |013E239A | 33C0 | xor eax,eax |013E239C | 5A | pop edx |013E239D | 59 | pop ecx |013E239E | 59 | pop ecx |013E239F | 64:8910 | mov dword ptr fs:[eax],edx |013E23A2 | 68 C5233E01 | push helpman.13E23C5 |013E23A7 | A1 B03A4601 | mov eax,dword ptr ds:[1463AB0] |013E23AC | 8B00 | mov eax,dword ptr ds:[eax] |013E23AE | 8B15 B03A4601 | mov edx,dword ptr ds:[1463AB0] |013E23B4 | 33C9 | xor ecx,ecx |013E23B6 | 890A | mov dword ptr ds:[edx],ecx |013E23B8 | E8 5B3A02FF | call helpman.405E18 |013E23BD | C3 | ret |013E23BE | E9 354B02FF | jmp helpman.406EF8 |013E23C3 | EB E2 | jmp helpman.13E23A7 |013E23C5 | 33C0 | xor eax,eax |013E23C7 | 5A | pop edx |013E23C8 | 59 | pop ecx |013E23C9 | 59 | pop ecx |013E23CA | 64:8910 | mov dword ptr fs:[eax],edx |013E23CD | 68 F0233E01 | push helpman.13E23F0 |013E23D2 | A1 185A4601 | mov eax,dword ptr ds:[1465A18] |013E23D7 | 8B00 | mov eax,dword ptr ds:[eax] |013E23D9 | 8B15 185A4601 | mov edx,dword ptr ds:[1465A18] |013E23DF | 33C9 | xor ecx,ecx |013E23E1 | 890A | mov dword ptr ds:[edx],ecx |013E23E3 | E8 303A02FF | call helpman.405E18 |013E23E8 | C3 | ret |013E23E9 | E9 0A4B02FF | jmp helpman.406EF8 |013E23EE | EB E2 | jmp helpman.13E23D2 |013E23F0 | 33C0 | xor eax,eax |013E23F2 | 5A | pop edx |013E23F3 | 59 | pop ecx |013E23F4 | 59 | pop ecx |013E23F5 | 64:8910 | mov dword ptr fs:[eax],edx |013E23F8 | 68 8D243E01 | push helpman.13E248D |013E23FD | A1 94404601 | mov eax,dword ptr ds:[1464094] |013E2402 | 8038 00 | cmp byte ptr ds:[eax],0 |013E2405 | 74 05 | je helpman.13E240C |013E2407 | E8 98CF02FF | call <JMP.&FreeConsole> |013E240C | C3 | ret |013E240D | E9 E64A02FF | jmp helpman.406EF8 |013E2412 | EB E9 | jmp helpman.13E23FD |013E2414 | 8B0D BC574601 | mov ecx,dword ptr ds:[14657BC] | 然后向下执行4句013E241A | 8B09 | mov ecx,dword ptr ds:[ecx] |013E241C | B2 01 | mov dl,1 |013E241E | A1 3CE7F000 | mov eax,dword ptr ds:[F0E73C] | 00F0E73C:&"砾D"

第3章
[Asm] 纯文本查看 复制代码
009851C2 | E8 F50BF2FF | call <原版helpman.sub_8A5DBC> |009851C7 | 837D F0 00 | cmp dword ptr ss:[ebp-10],0 | [ebp-10]:L"HMLIC"009851CB | 0F84 F5000000 | je 原版helpman.9852C6 |009851D1 | 33C0 | xor eax,eax |009851D3 | 8943 70 | mov dword ptr ds:[ebx+70],eax |009851D6 | 8D95 98FDFFFF | lea edx,dword ptr ss:[ebp-268] | [ebp-268]:L"\\SOFTWARE\\ECSOFTWARE\\Help+Manual 8"009851DC | 8B45 F4 | mov eax,dword ptr ss:[ebp-C] | [ebp-C]:&L"Help+Manual 8"009851DF | E8 58E8FFFF | call <原版helpman.sub_983A3C> |009851E4 | 8B85 98FDFFFF | mov eax,dword ptr ss:[ebp-268] | [ebp-268]:L"\\SOFTWARE\\ECSOFTWARE\\Help+Manual 8"009851EA | 8D8D 9CFDFFFF | lea ecx,dword ptr ss:[ebp-264] |009851F0 | BA CC549800 | mov edx,<原版helpman.&sub_6C0041> | 9854CC:L"AlternateBaseURL"009851F5 | E8 1EE1FFFF | call 原版helpman.983318 |009851FA | 8B85 9CFDFFFF | mov eax,dword ptr ss:[ebp-264] |00985200 | 8D55 F8 | lea edx,dword ptr ss:[ebp-8] |00985203 | E8 082AADFF | call <原版helpman.sub_457C10> |00985208 | 837D F8 00 | cmp dword ptr ss:[ebp-8],0 |0098520C | 0F84 A8000000 | je 原版helpman.9852BA |00985212 | BA FC549800 | mov edx,原版helpman.9854FC | 9854FC:L"^(https:\\/\\/)[-A-Za-z0-9+&#/%?=~_|!:,.;]+[-A-Za-z0-9+&#/%=~_|]$"00985217 | 8B45 F8 | mov eax,dword ptr ss:[ebp-8] |0098521A | E8 11B7EDFF | call 原版helpman.860930 |0098521F | 84C0 | test al,al |00985221 | 0F84 93000000 | je 原版helpman.9852BA |00985227 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |0098522C | 8B55 F8 | mov edx,dword ptr ss:[ebp-8] |0098522F | E8 F465A8FF | call 原版helpman.40B828 |00985234 | EB 2B | jmp 原版helpman.985261 |00985236 | 8B35 FC957502 | mov esi,dword ptr ds:[27595FC] | esi:sub_2662D8C+2C0098523C | 8B36 | mov esi,dword ptr ds:[esi] | esi:sub_2662D8C+2C0098523E | 85F6 | test esi,esi | esi:sub_2662D8C+2C00985240 | 74 05 | je 原版helpman.985247 |00985242 | 83EE 04 | sub esi,4 | esi:sub_2662D8C+2C00985245 | 8B36 | mov esi,dword ptr ds:[esi] | esi:sub_2662D8C+2C00985247 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |0098524C | 50 | push eax |0098524D | 8BCE | mov ecx,esi | esi:sub_2662D8C+2C0098524F | 49 | dec ecx |00985250 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |00985255 | 8B00 | mov eax,dword ptr ds:[eax] |00985257 | BA 01000000 | mov edx,1 |0098525C | E8 3B78A8FF | call <原版helpman.sub_40CA9C> |00985261 | 8D85 94FDFFFF | lea eax,dword ptr ss:[ebp-26C] |00985267 | 50 | push eax |00985268 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |0098526D | 8B00 | mov eax,dword ptr ds:[eax] |0098526F | E8 CC66A8FF | call <原版helpman.sub_40B940> |00985274 | 8BD0 | mov edx,eax |00985276 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |0098527B | 8B00 | mov eax,dword ptr ds:[eax] |0098527D | B9 01000000 | mov ecx,1 |00985282 | E8 1578A8FF | call <原版helpman.sub_40CA9C> |00985287 | 8B85 94FDFFFF | mov eax,dword ptr ss:[ebp-26C] |0098528D | BA 88559800 | mov edx,原版helpman.985588 |00985292 | E8 CD77A8FF | call <原版helpman.sub_40CA64> |00985297 | 74 9D | je 原版helpman.985236 |00985299 | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |0098529E | 8B00 | mov eax,dword ptr ds:[eax] |009852A0 | BA FC549800 | mov edx,原版helpman.9854FC | 9854FC:L"^(https:\\/\\/)[-A-Za-z0-9+&#/%?=~_|!:,.;]+[-A-Za-z0-9+&#/%=~_|]$"009852A5 | E8 86B6EDFF | call 原版helpman.860930 |009852AA | 84C0 | test al,al |009852AC | 75 1F | jne 原版helpman.9852CD |009852AE | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |009852B3 | E8 9061A8FF | call <原版helpman.sub_40B448> |009852B8 | EB 13 | jmp 原版helpman.9852CD |009852BA | A1 FC957502 | mov eax,dword ptr ds:[27595FC] |009852BF | E8 8461A8FF | call <原版helpman.sub_40B448> |009852C4 | EB 07 | jmp 原版helpman.9852CD |009852C6 | C743 70 01000000 | mov dword ptr ds:[ebx+70],1 |009852CD | 8B45 FC | mov eax,dword ptr ss:[ebp-4] |009852D0 | 8943 50 | mov dword ptr ds:[ebx+50],eax |009852D3 | 8BC3 | mov eax,ebx | ebx:&L"Help+Manual 8"009852D5 | 8B55 F4 | mov edx,dword ptr ss:[ebp-C] | [ebp-C]:&L"Help+Manual 8"009852D8 | 8B0D A0349800 | mov ecx,dword ptr ds:[9834A0] |009852DE | E8 4581A8FF | call <原版helpman.sub_40D428> |009852E3 | 8D43 08 | lea eax,dword ptr ds:[ebx+8] | [ebx+8]:L"HM"009852E6 | 8BD7 | mov edx,edi | edi:L"HM"009852E8 | E8 3B65A8FF | call 原版helpman.40B828 |009852ED | 8D43 0C | lea eax,dword ptr ds:[ebx+C] | [ebx+C]:L"HMLIC"009852F0 | 8B55 F0 | mov edx,dword ptr ss:[ebp-10] | [ebp-10]:L"HMLIC"009852F3 | E8 3065A8FF | call 原版helpman.40B828 |009852F8 | 8D85 90FDFFFF | lea eax,dword ptr ss:[ebp-270] |009852FE | E8 0990EEFF | call 原版helpman.86E30C |00985303 | 8B95 90FDFFFF | mov edx,dword ptr ss:[ebp-270] |00985309 | 8D43 14 | lea eax,dword ptr ds:[ebx+14] |0098530C | E8 B7A4A8FF | call 原版helpman.40F7C8 |00985311 | E8 AA83ADFF | call <原版helpman.sub_45D6C0> | 像!====================================================01C8F1DC | 68 F1F1C801 | push <原版helpman.sub_1C8F1F1> |01C8F1E1 | 8B45 EC | mov eax,dword ptr ss:[ebp-14] | [ebp-14]:&"CRC=\\software\\Microsoft\\Internet Account Manager\\Accounts"01C8F1E4 | E8 C3A377FE | call <原版helpman.sub_4095AC> |01C8F1E9 | C3 | ret |01C8F1EA | E9 C1B677FE | jmp 原版helpman.40A8B0 |01C8F1EF | EB F0 | jmp <原版helpman.sub_1C8F1E1> |01C8F1F1 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"01C8F1F4 | 8B40 68 | mov eax,dword ptr ds:[eax+68] |01C8F1F7 | BA 74F4C801 | mov edx,<原版helpman.sub_1C8F474> | 1C8F474:"lang1033.txt"01C8F1FC | E8 B3F3FFFF | call 原版helpman.1C8E5B4 |01C8F201 | 8BD0 | mov edx,eax |01C8F203 | 8B45 FC | mov eax,dword ptr ss:[ebp-4] | [ebp-4]:&"劋S"01C8F206 | 8B80 94000000 | mov eax,dword ptr ds:[eax+94] |01C8F20C | 8B08 | mov ecx,dword ptr ds:[eax] |01C8F20E | FF51 6C | call dword ptr ds:[ecx+6C] |01C8F211 | 8D85 94FDFFFF | lea eax,dword ptr ss:[ebp-26C] |01C8F217 | 50 | push eax |01C8F218 | 8D95 40FDFFFF | lea edx,dword ptr ss:[ebp-2C0] | [ebp-2C0]:L"X:\\HelpAndManual8\\原版HELPMAN.EXE"01C8F21E | A1 B0AF7502 | mov eax,dword ptr ds:[275AFB0] |01C8F223 | 8B00 | mov eax,dword ptr ds:[eax] |01C8F225 | E8 7696A2FE | call 原版helpman.6B88A0 |01C8F22A | 8B85 40FDFFFF | mov eax,dword ptr ss:[ebp-2C0] | [ebp-2C0]:L"X:\\HelpAndManual8\\原版HELPMAN.EXE"01C8F230 | E8 2BD477FE | call <原版helpman.sub_40C660> |01C8F235 | 50 | push eax |01C8F236 | E8 D19F78FE | call <JMP.&FindFirstFileW> |01C8F23B | 8BD8 | mov ebx,eax |01C8F23D | 85DB | test ebx,ebx |01C8F23F | 74 5C | je 原版helpman.1C8F29D |01C8F241 | 8D85 98FDFFFF | lea eax,dword ptr ss:[ebp-268] |01C8F247 | 8945 E8 | mov dword ptr ss:[ebp-18],eax |01C8F24A | 8D85 84FDFFFF | lea eax,dword ptr ss:[ebp-27C] | [ebp-27C]:L"-0"01C8F250 | 50 | push eax |01C8F251 | 8B45 E8 | mov eax,dword ptr ss:[ebp-18] |01C8F254 | 50 | push eax |01C8F255 | E8 9A9F78FE | call <JMP.&FileTimeToSystemTime>=======================>01C8F25A | 8D85 84FDFFFF | lea eax,dword ptr ss:[ebp-27C] | [ebp-27C]:L"-0"01C8F260 | E8 6BE37CFE | call <原版helpman.sub_45D5D0> |01C8F265 | DD1D 70A97A02 | fstp qword ptr ds:[27AA970],st(0) |01C8F26B | 9B | fwait |01C8F26C | 8D85 A8FDFFFF | lea eax,dword ptr ss:[ebp-258] |01C8F272 | 8945 E4 | mov dword ptr ss:[ebp-1C],eax |01C8F275 | 8D85 84FDFFFF | lea eax,dword ptr ss:[ebp-27C] | [ebp-27C]:L"-0"01C8F27B | 50 | push eax |01C8F27C | 8B45 E4 | mov eax,dword ptr ss:[ebp-1C] |01C8F27F | 50 | push eax |01C8F280 | E8 6F9F78FE | call <JMP.&FileTimeToSystemTime> |01C8F285 | 8D85 84FDFFFF | lea eax,dword ptr ss:[ebp-27C] | [ebp-27C]:L"-0"01C8F28B | E8 40E37CFE | call <原版helpman.sub_45D5D0> |01C8F290 | DD1D 78A97A02 | fstp qword ptr ds:[27AA978],st(0) |01C8F296 | 9B | fwait |01C8F297 | 53 | push ebx |01C8F298 | E8 679F78FE | call <JMP.&FindClose> |01C8F29D | E8 1EE47CFE | call <原版helpman.sub_45D6C0> ===>里边是多个GetLocalTime的调用点

第4章
第5章过期后,有意思的是文档会为只读。
由于我知道该软件使用了RichViewEdit控件,因此查询一下帮助该方法的实现。
配图
我们就可以用Delphi 11.2 + RichViewEdit控件编程来模拟实现。
[Delphi] 纯文本查看 复制代码
procedure TForm4.Button1Click(Sender: TObject);begin RichViewEdit1.ReadOnly := True; //只读end;
[Delphi] 纯文本查看 复制代码
procedure TForm4.Button1Click(Sender: TObject);beginRichViewEdit1.ReadOnly := False; //取消只读end;

用IDR分别打开两份,对比一下机器码一目了然吧?

回到x64dbg中,Ctrl+B定位修改OK了吧?只有call的那一行不一样。
配图
第6章
配图

第7章
配图
又过了数月,意外在某QQ群中的某群文件中发现了一个控件名字很有意思
索性上网搜索下吧,一看界面和实现的功能,马上一切疑问一扫而空,天亮了下雪了。。。
第8章 额外的启迪与思考

配图
额外的RichViewEdit插件
额外的库pdfium.dll接口
额外的调试输出日志插件
这些调用方法,法王姥爷你编程都掌握了么?
后记:该软件作为Delphi开发的软件还是相当牛逼的。具体表现在几个方面:
- 功能比较完备
- 授权机制中规中矩
- 使用了特殊的日志与堆栈输出控件
- 有网络校验
- 功能限制方面做得可圈可点,对Delphi老粉来说是个非常好的素材和模仿对象
如果12分是满分的话,至少我给他打11分。

再说下缺陷吧:正是因为上面的第三点才更快的被破解者找到堆栈调用地址,一击必杀。
我觉得作者这么做还是存在争议的。
华山资源网 Design By www.eoogi.com
广告合作:本站广告合作请联系QQ:858582 申请时备注:广告合作(否则不回)
免责声明:本站资源来自互联网收集,仅供用于学习和交流,请遵循相关法律法规,本站一切资源不代表本站立场,如有侵权、后门、不妥请联系本站删除!
免责声明:本站资源来自互联网收集,仅供用于学习和交流,请遵循相关法律法规,本站一切资源不代表本站立场,如有侵权、后门、不妥请联系本站删除!
华山资源网 Design By www.eoogi.com
暂无评论...
《魔兽世界》大逃杀!60人新游玩模式《强袭风暴》3月21日上线
暴雪近日发布了《魔兽世界》10.2.6 更新内容,新游玩模式《强袭风暴》即将于3月21 日在亚服上线,届时玩家将前往阿拉希高地展开一场 60 人大逃杀对战。
艾泽拉斯的冒险者已经征服了艾泽拉斯的大地及遥远的彼岸。他们在对抗世界上最致命的敌人时展现出过人的手腕,并且成功阻止终结宇宙等级的威胁。当他们在为即将于《魔兽世界》资料片《地心之战》中来袭的萨拉塔斯势力做战斗准备时,他们还需要在熟悉的阿拉希高地面对一个全新的敌人──那就是彼此。在《巨龙崛起》10.2.6 更新的《强袭风暴》中,玩家将会进入一个全新的海盗主题大逃杀式限时活动,其中包含极高的风险和史诗级的奖励。
《强袭风暴》不是普通的战场,作为一个独立于主游戏之外的活动,玩家可以用大逃杀的风格来体验《魔兽世界》,不分职业、不分装备(除了你在赛局中捡到的),光是技巧和战略的强弱之分就能决定出谁才是能坚持到最后的赢家。本次活动将会开放单人和双人模式,玩家在加入海盗主题的预赛大厅区域前,可以从强袭风暴角色画面新增好友。游玩游戏将可以累计名望轨迹,《巨龙崛起》和《魔兽世界:巫妖王之怒 经典版》的玩家都可以获得奖励。
更新日志
2024年12月22日
2024年12月22日
- 小骆驼-《草原狼2(蓝光CD)》[原抓WAV+CUE]
- 群星《欢迎来到我身边 电影原声专辑》[320K/MP3][105.02MB]
- 群星《欢迎来到我身边 电影原声专辑》[FLAC/分轨][480.9MB]
- 雷婷《梦里蓝天HQⅡ》 2023头版限量编号低速原抓[WAV+CUE][463M]
- 群星《2024好听新歌42》AI调整音效【WAV分轨】
- 王思雨-《思念陪着鸿雁飞》WAV
- 王思雨《喜马拉雅HQ》头版限量编号[WAV+CUE]
- 李健《无时无刻》[WAV+CUE][590M]
- 陈奕迅《酝酿》[WAV分轨][502M]
- 卓依婷《化蝶》2CD[WAV+CUE][1.1G]
- 群星《吉他王(黑胶CD)》[WAV+CUE]
- 齐秦《穿乐(穿越)》[WAV+CUE]
- 发烧珍品《数位CD音响测试-动向效果(九)》【WAV+CUE】
- 邝美云《邝美云精装歌集》[DSF][1.6G]
- 吕方《爱一回伤一回》[WAV+CUE][454M]
